Kubernetes Dashboard it’s really helpfull for sharing the URL with team mate or anyone, because by share the URL we can see the same thing. We don’t need to ask people to open their terminal and poking around looking for logs.
prerequisite:
– Kubernetes cluster
– helm
– kubectl
Create a namespace monitoring for a dedicated monitoring and it’s tools. But you can use any namespace
kubectl create namespace monitoring
helm pull kubernetes-dashboard/kubernetes-dashboardit’ll download the latest kubernetes-dashboard helm chart to current directory, the current latest version is kubernetes-dashboard-6.0.8.tgz, which use dashboard v2.7.0. Extract the directory
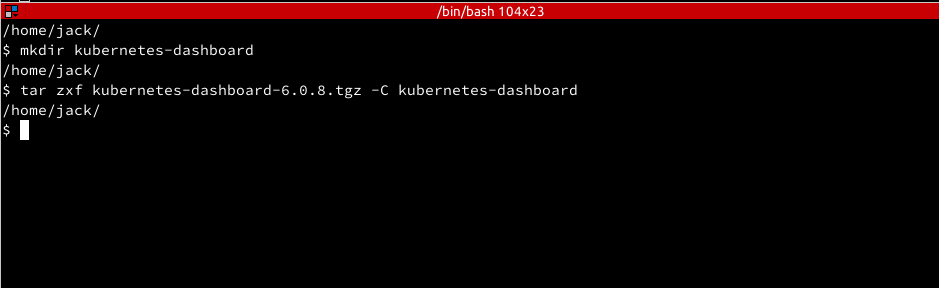
tar zxvf kubernetes-dashboard-6.0.8.tgzcreate a folder to store the helm chart, then extract the files inside tgz there
mkdir kubernetes-dashboard tar zxf kubernetes-dashboard-6.0.8.tgz -C kubernetes-dashboard
Update values.yaml
Update the values.yaml as follow
rbac: clusterReadOnlyRole: true extraArgs: - --enable-skip-login - --enable-insecure-login
clusterReadOnlyRole it’ll create a read-only roles for dashboard-kubernetes roles.
enable-skip-login this option to allow user to access Kubernetes Dashboard UI without need to enter the token or kubeconfig
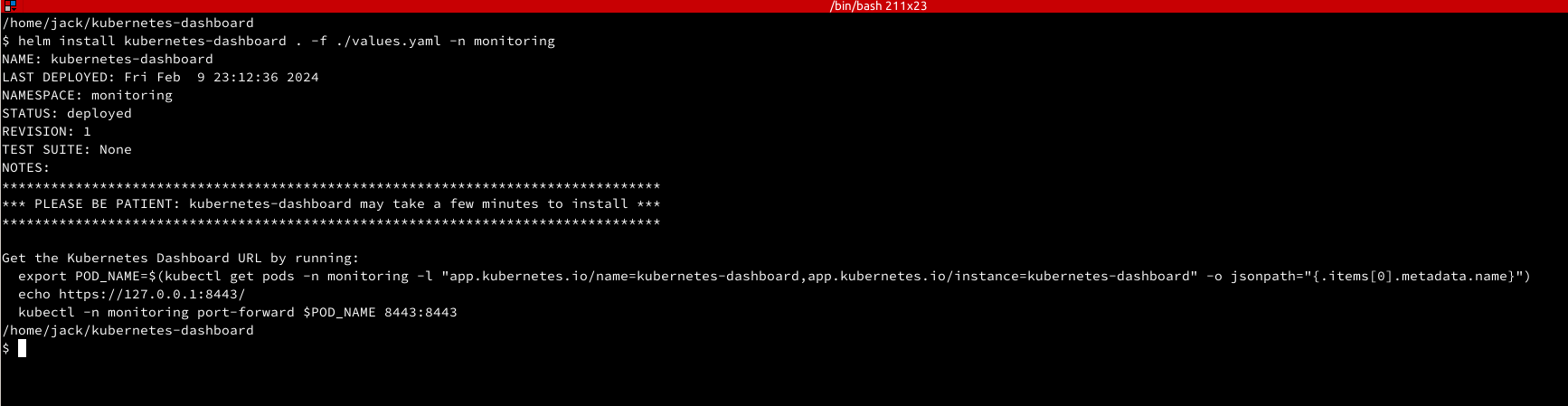
For the first install use helm install, later we can update the the values and template
helm install kubernetes-dashboard . -f ./values.yaml -n monitoring
Access the UI
From terminal setup the port forward
export POD_NAME=$(kubectl get pods -n monitoring -l "app.kubernetes.io/name=kubernetes-dashboard,app.kubernetes.io/instance=kubernetes-dashboard" -o jsonpath="{.items[0].metadata.name}") kubectl -n monitoring port-forward $POD_NAME 8443:8443
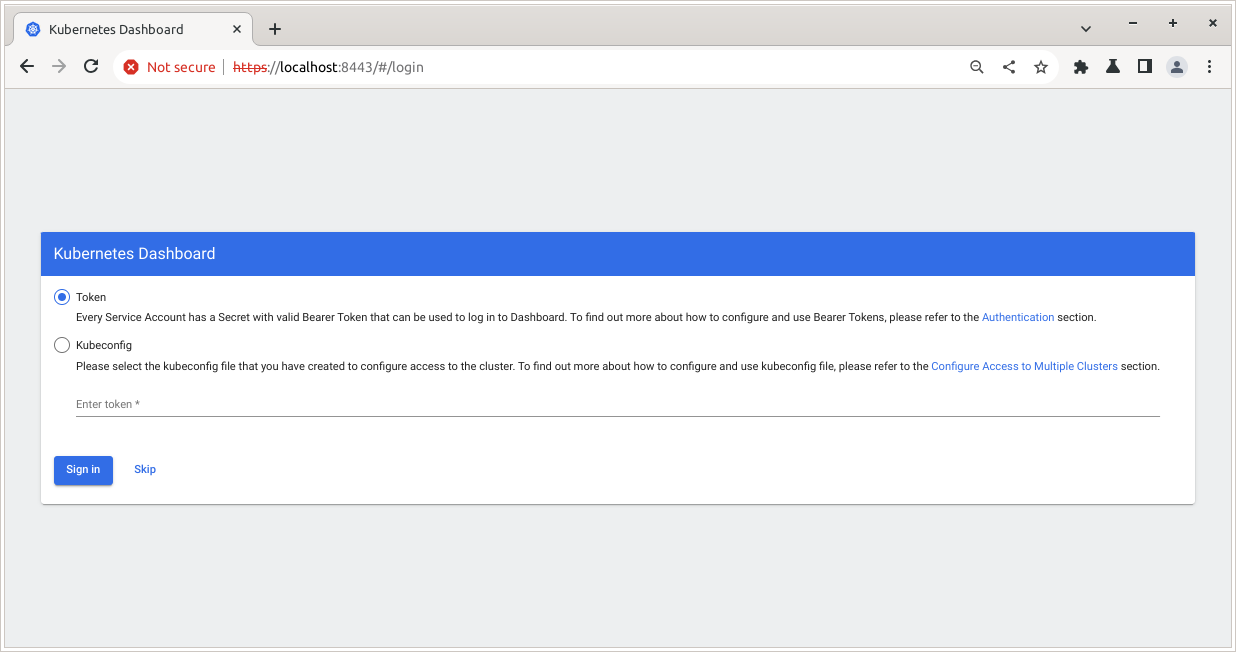
then from the browser open https://localhost:8443
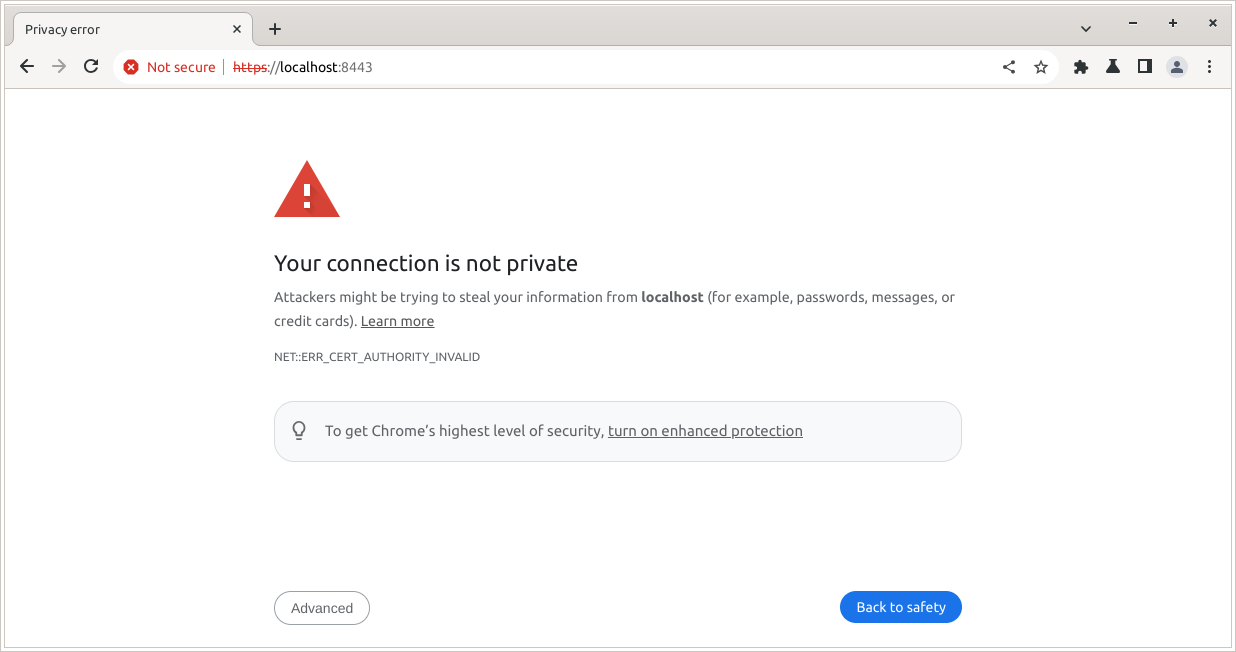
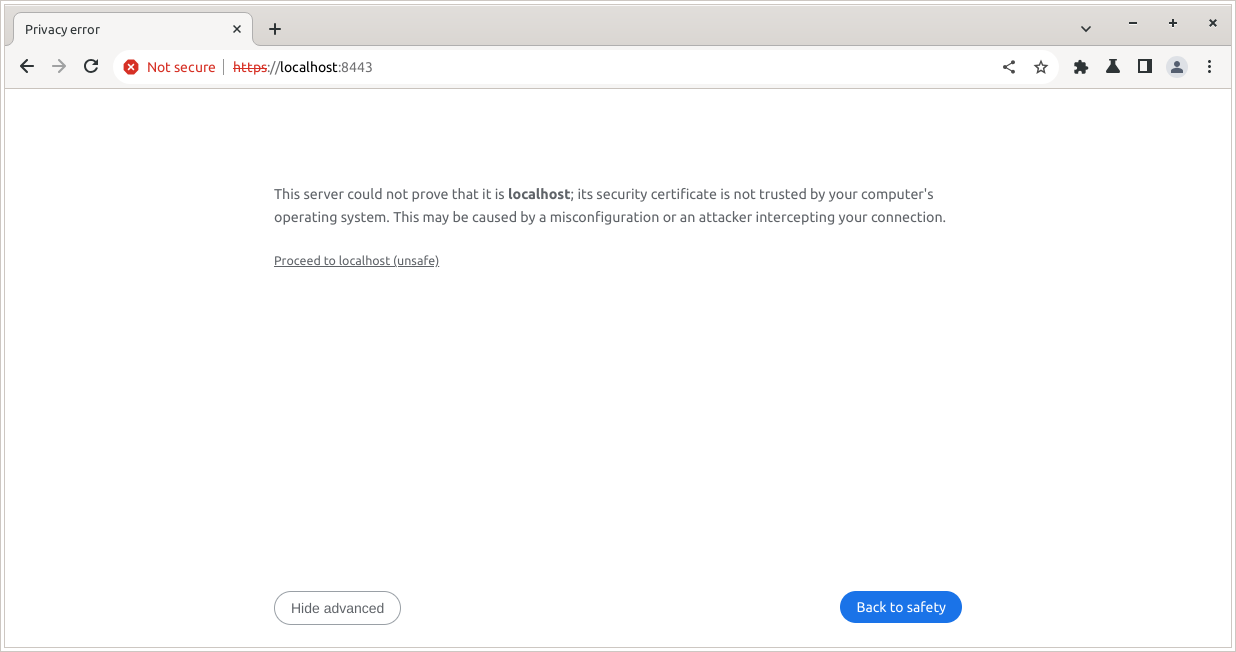
For development/testing it’s okay to ignore that error, click Advanced -> Proceed to localhost (unsafe)
In the next windows, click Skip
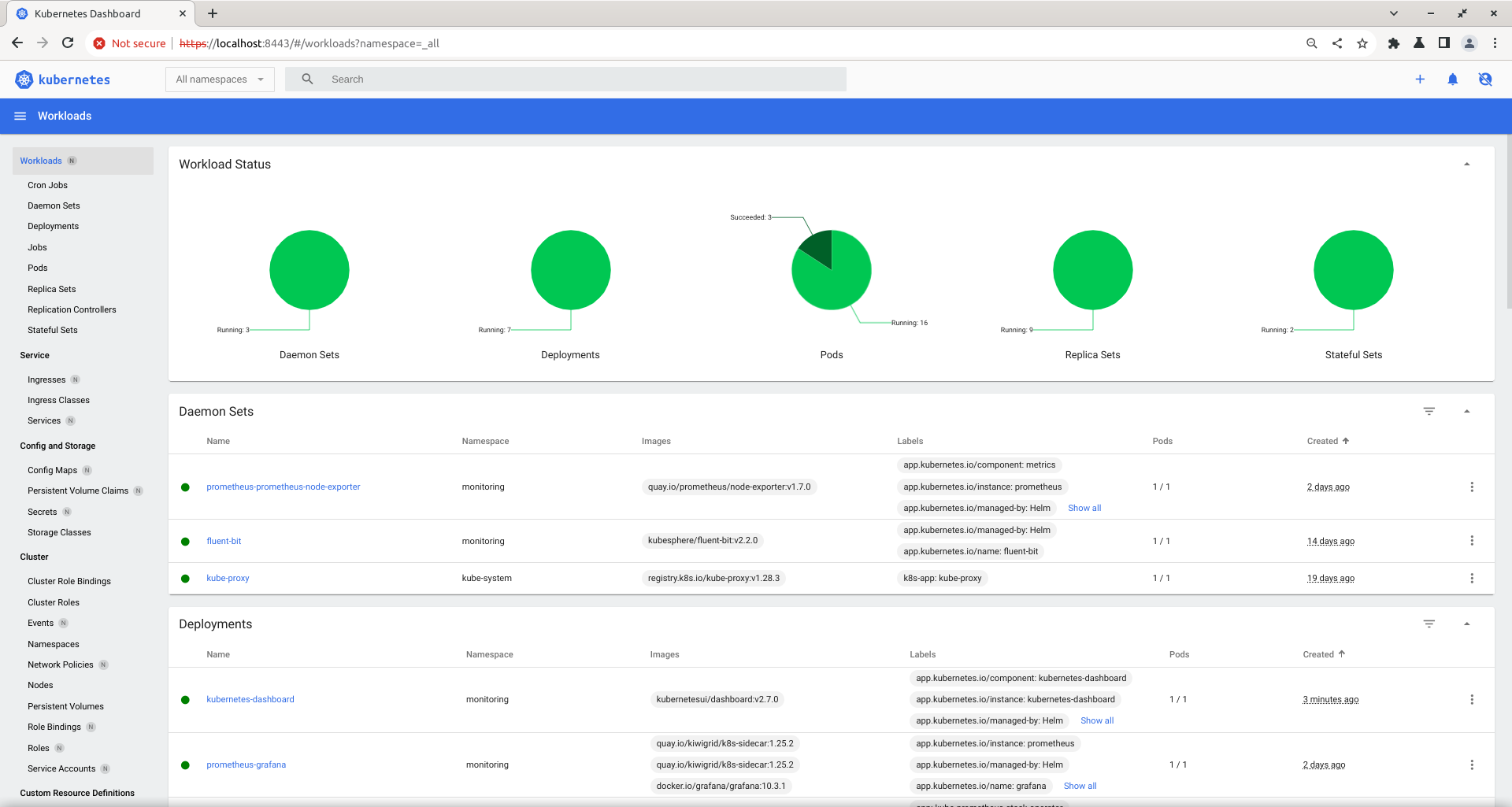
It’s working, but all the we need to reduces the access to secrets and roles. Because that object store a lot of sensitive information, so we need to skip if for obvious reason.
Limit the Access
Kubernetes had 2 different role, role and clusterrole. role for certain namespace only, for example namespace monitoring, and clusterrole for the whole cluster. Kubernetes dashboard helm chart had both of them, for the roles it’s under ClusterRole, so we’ll update the it on the template. Open template/clusterrole-readonly.yaml remove
- apiGroups:
- rbac.authorization.k8s.io
resources:
- clusterrolebindings
- clusterroles
- roles
- rolebindings
verbs:
- get
- list
- watchThen deploy the helm chart again
helm upgrade --install kubernetes-dashboard . -f ./values.yaml -n monitoring # output Release "kubernetes-dashboard" has been upgraded. Happy Helming! NAME: kubernetes-dashboard LAST DEPLOYED: Fri Feb 9 23:36:32 2024 NAMESPACE: monitoring STATUS: deployed REVISION: 2 TEST SUITE: None